For the C-Suite: The biggest hidden risk in cloud SaaS is "Logical Separation." Most vendors dump all their clients' data into one massive database and use software filters to keep it apart. If that filter fails, Bank A sees Bank B’s data.
NUMR CXM rejects this model.
As a leader in the BFSI space, you have likely asked SaaS vendors this question: "Will my sensitive financial data be stored alongside my competitors?"
Usually, the answer is a vague "Yes, but it's logically separated."
In the SaaS world, this is called Multi-Tenancy. It means your customer's loan applications are sitting in the same database table as another bank's data, separated only by a Customer_ID tag in the code. A single bug in that code could expose your proprietary data to the wrong eyes.
For a retail app, that’s a bug. For a bank, that’s a headline-making disaster.
“Security in the cloud is fundamentally about isolation ensuring one customer’s workload can never impact another’s.”
– Andy Jassy
This principle sits at the core of modern BFSI cloud security architecture. Financial institutions cannot rely solely on logical controls layered on shared infrastructure. NUMR CXM’s single-tenant data isolation model eliminates the traditional multi-tenant exposure risk by physically separating banking datasets, ensuring that customer intelligence analytics operate within a fully isolated environment aligned with zero-trust security principles.
At NUMR CXM, we believe that "Logical Separation" is not enough for Financial Services. We built Physical Isolation into the bedrock of our platform.
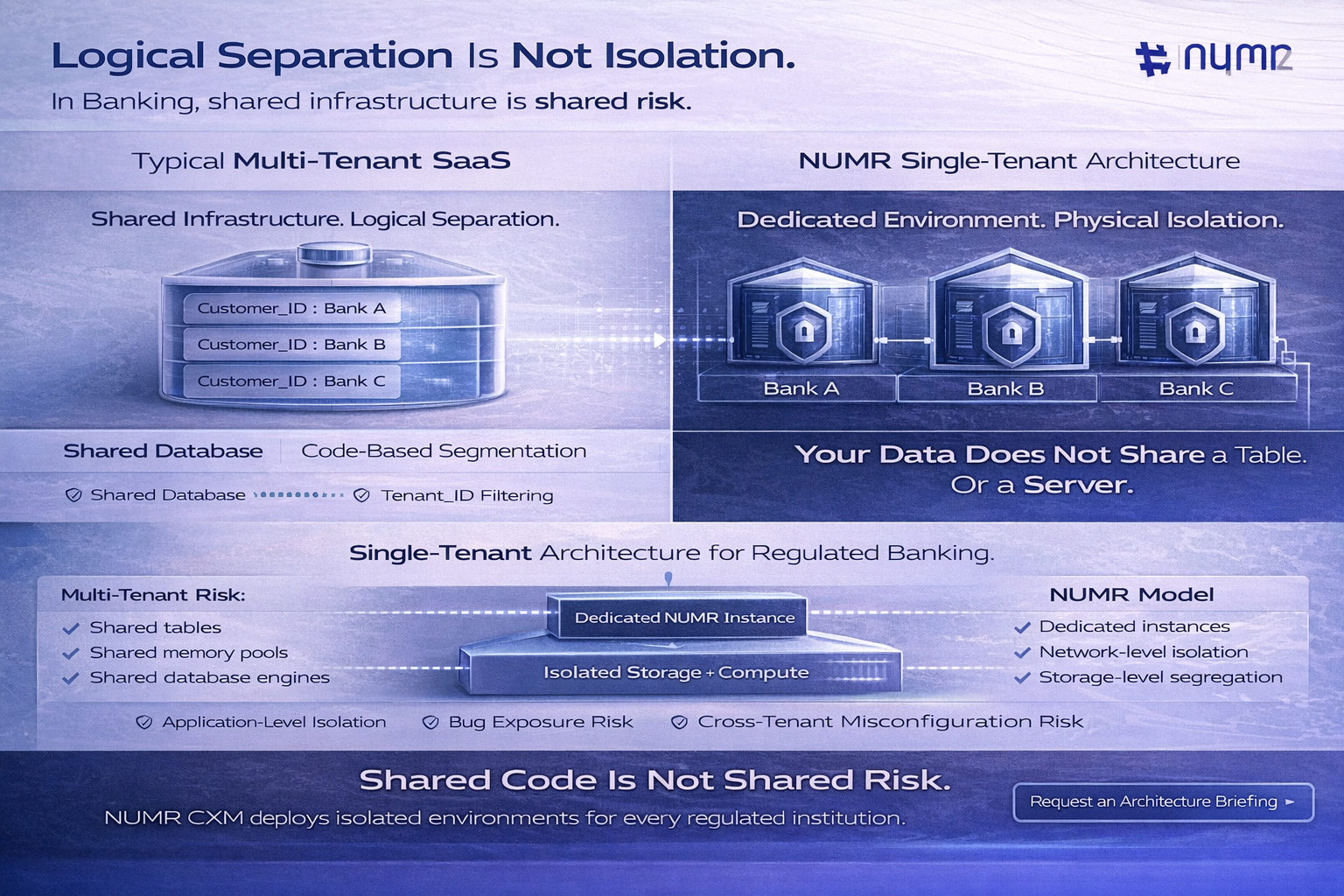
We treat every client as a distinct entity, not just a row in a spreadsheet. Our architecture enforces strict barriers between your environment and everyone else's.
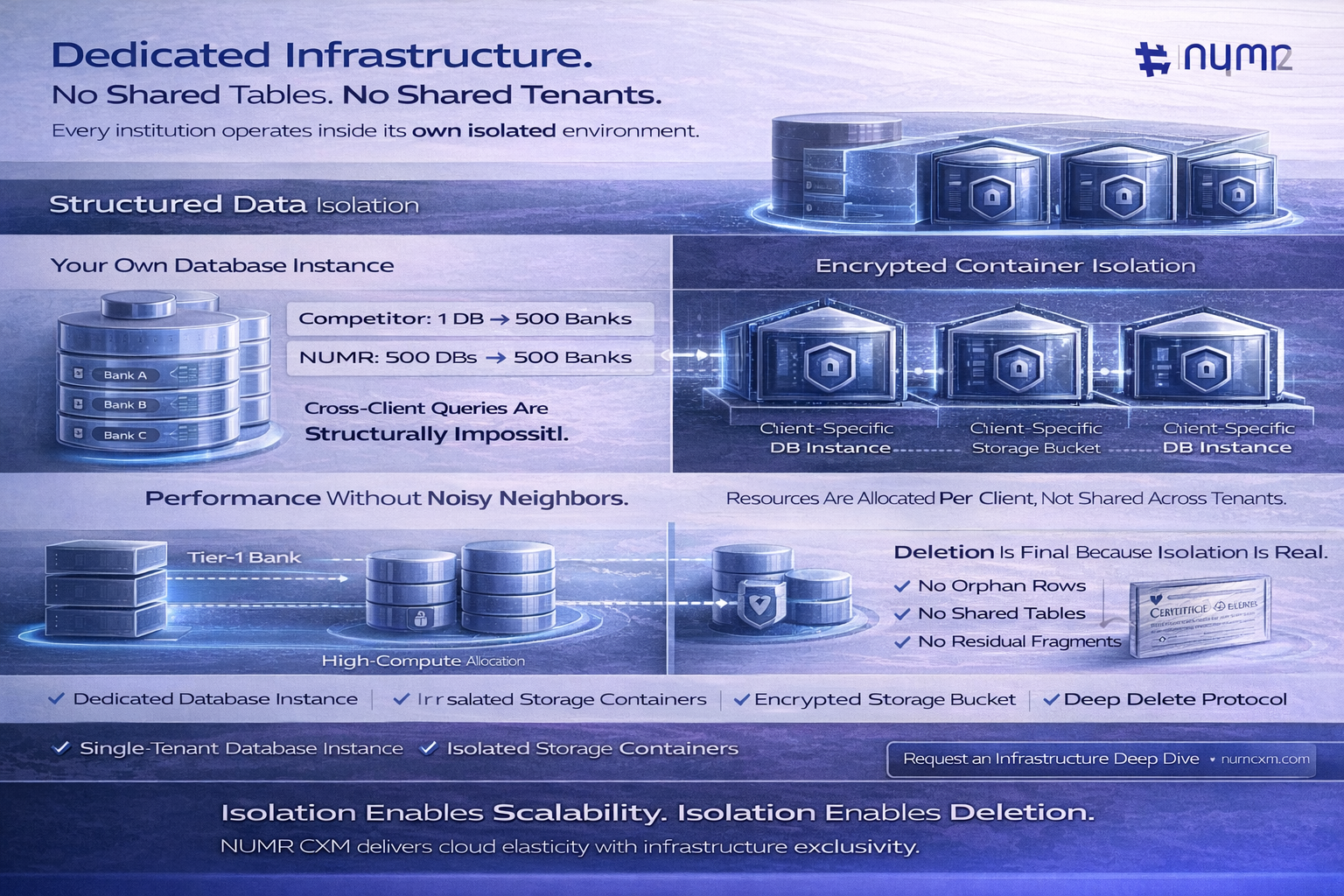
For all structured information (transaction logs, survey scores, customer metadata), we provision a dedicated database instance for your organization.
For heavy data like audio recordings, chat logs, and video feedback, we utilize isolated data containers.
This "Siloed Architecture" isn't just about security; it's about performance.
Because every client has their own database, we can tune the performance based on your specific load, without "noisy neighbors" slowing you down.
You get the scalability of the Cloud with the exclusivity of On-Premise.
“Hybrid and dedicated architectures allow organizations to innovate in the cloud without sacrificing performance isolation.”
– Thomas Kurian
NUMR CXM demonstrates how modern CX platforms can combine cloud scalability with isolated performance environments. By allocating independent resources per institution, banks avoid the classic ‘noisy neighbor’ problem, enabling predictable performance, secure analytics processing, and scalable customer experience intelligence tailored specifically for BFSI workloads.
One of the hardest things to do in a shared database is deleting data. When you cancel a contract with a typical SaaS vendor, they often just "soft delete" your data (hiding it from view) because scrubbing it permanently is too risky for the integrity of their shared tables.
NUMR CXM makes leaving as safe as joining.
Because your data lives in its own isolated house, we can bulldoze the house when you leave.
Don't let your data live in a shared house. Get the security of a private vault with the intelligence of a modern CX platform.
Q: Does having a separate database make the platform slower?
A: On the contrary, it makes it faster. Because your queries run against your own dedicated dataset, you aren't slowed down by other clients running complex reports on the same system.
Q: If we are isolated, how do we get platform updates?
A: Our application layer is global, but the data layer is isolated. You get all the latest AI features and bug fixes instantly, but those features apply only to your secluded data.
Q: Can you recover our data after the "Deep Delete"?
A: No. Once the Certificate of Deletion is issued, the encryption keys are destroyed and the storage blocks are overwritten. This is a safety feature, not a bug.
Q: Is this architecture compliant with GDPR and RBI data localization?
A: Yes. Isolation actually makes compliance easier. If a regulator asks where your data is, we can point to a specific, isolated box rather than a nebulous shared cloud.
In the BFSI sector, trust is binary. You either have it, or you don't. By ensuring Full Data Isolation, NUMR CXM removes the "Trust" variable from the equation entirely.
You don't have to trust that our code will keep your data separate - our physics does it for us.
Whether you are a massive institution or a digital challenger, your proprietary data remains exactly that: Proprietary.