TL;DR:
For the C-Suite: NUMR CXM isn't just a marketing tool; it’s a fortress for your financial data. We solve the "Innovation vs. Security" deadlock with an architecture designed specifically for banking compliance.
Zero-Trust Tokenization: We replace sensitive PII with useless tokens before analysis, ensuring customer identities are never exposed to raw processing.
Bank-Grade Encryption: Your data is locked with AES-256 encryption at rest and in motion - making it readable only to you.
Total Sovereignty (BYOK): You hold the encryption keys. If you ever leave, you revoke the key, and the data is cryptographically shredded instantly.
Compliance Ready: Built to satisfy GDPR, CCPA, and strict internal banking audits from Day 1.
The Bottom Line: You get world-class CX intelligence without compromising a single byte of customer trust.
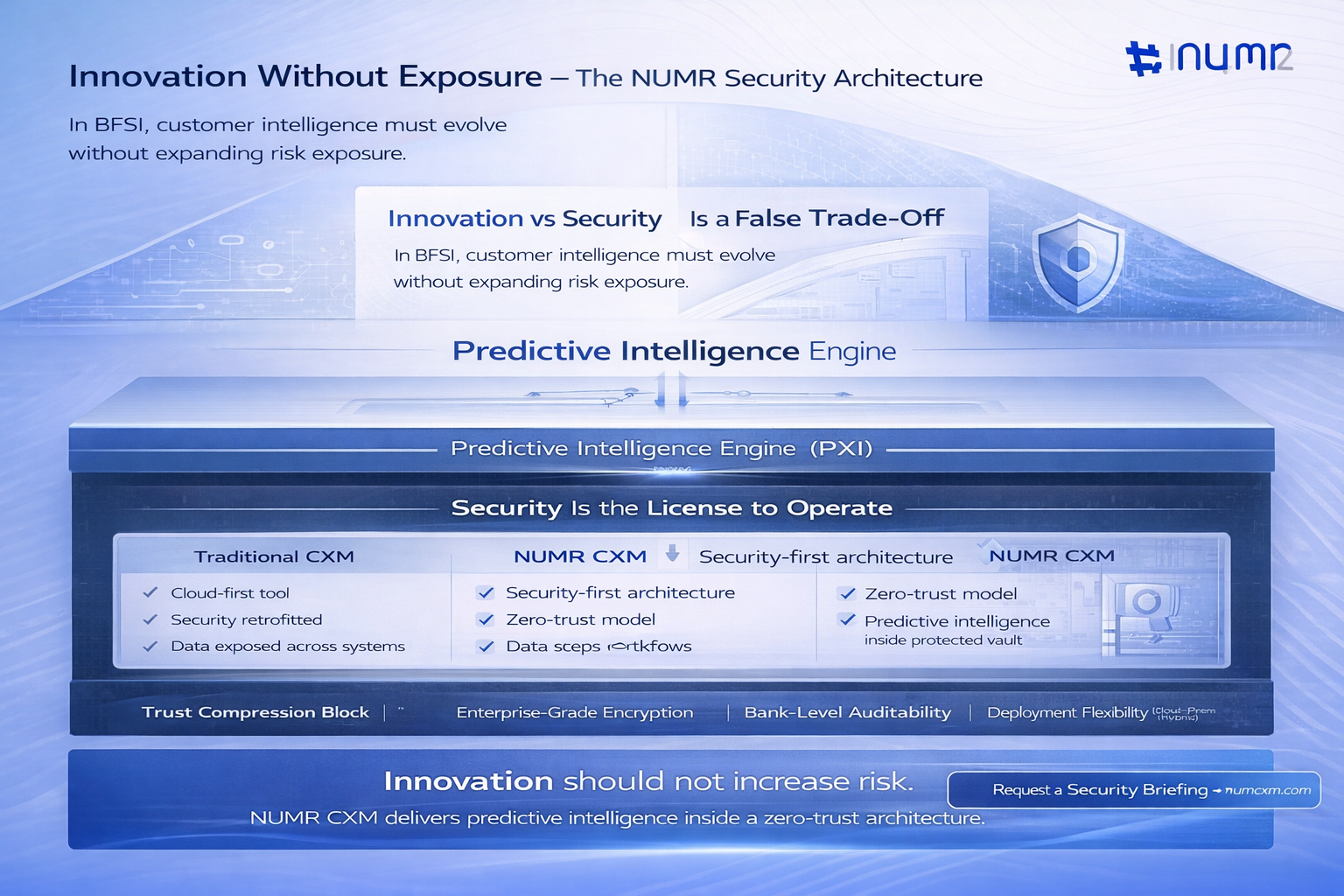
For a Chief Experience Officer (CXO) or VP in the BFSI sector, the mandate is contradictory: Move faster to capture digital-first customers, but lock everything down to satisfy risk and compliance.
You are likely evaluating Customer Experience Management (CXM) platforms to decode customer behavior and drive revenue.
But the moment you mention "cloud," "AI," or "customer data," your CISO’s alarm bells ring. And rightly so. In Fintech and Banking, data isn’t just an asset; it is a liability if mishandled.
According to Deloitte, financial institutions must embed cybersecurity directly into digital innovation rather than treating security as a downstream control.
This insight directly reflects the modern Innovation vs Security paradox in BFSI. Banks pursuing digital transformation require CXM platforms that deliver customer intelligence without increasing risk exposure. NUMR CXM’s zero-trust security architecture, encryption standards, and compliance-first design ensure that customer experience analytics and banking data protection evolve together, allowing innovation without compromising regulatory security requirements.
At NUMR CXM, we understand that for financial institutions, security isn't a "feature" - it is the license to operate. We didn't build a marketing tool and add a firewall later.
We architected a bank-grade data vault that happens to possess world-class predictive intelligence.
Here is the architectural reality of how we protect your data, ensuring you sleep as soundly as your compliance officer.
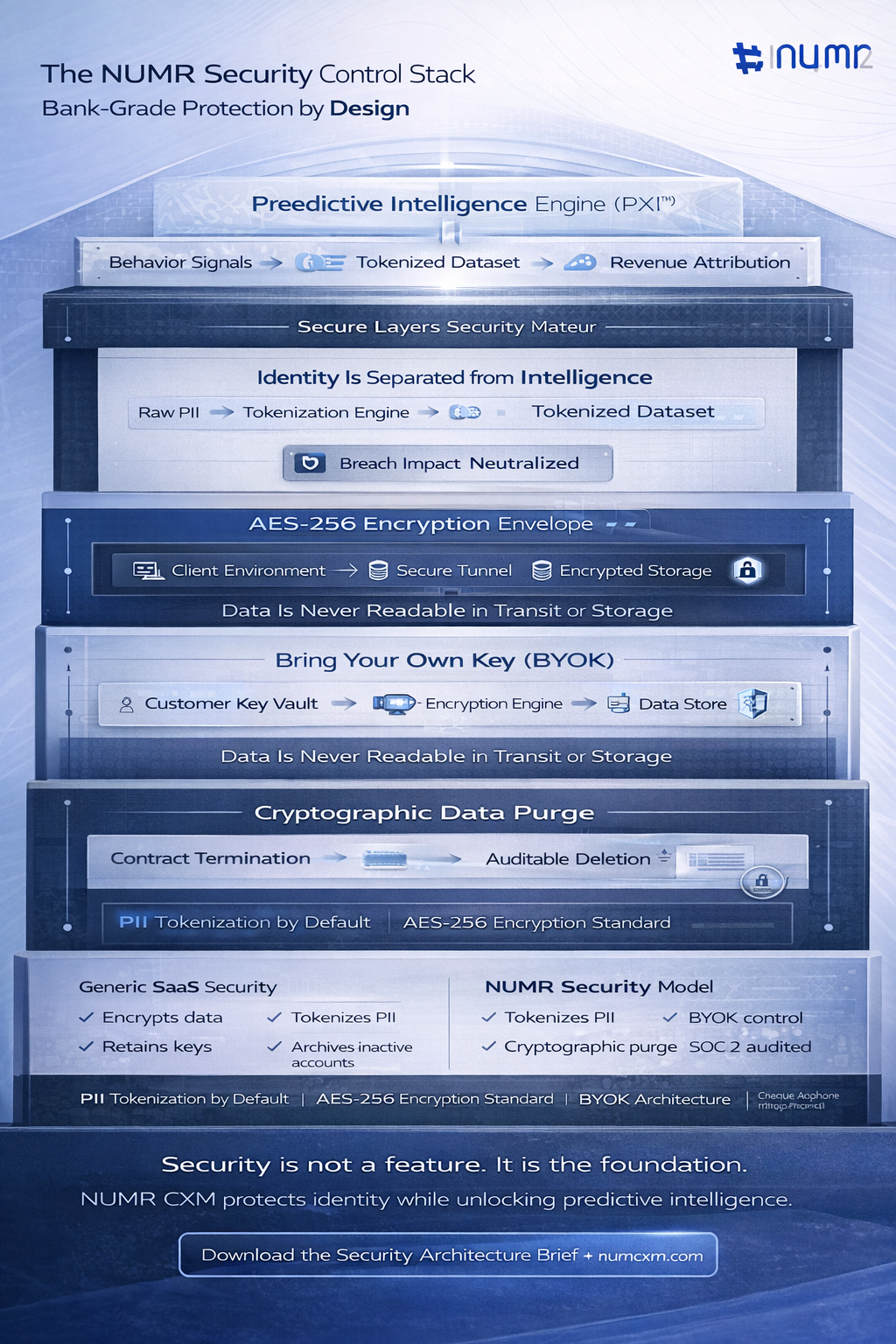
The biggest risk in CXM is the exposure of Personally Identifiable Information (PII). Most platforms encrypt this data, but if a key is compromised, the data is readable.
NUMR CXM adopts a Tokenization-First Strategy.
The IBM Security reports that tokenization significantly reduces breach impact because stolen data tokens contain no exploitable personal information.
This validates why PII tokenization in CXM platforms is becoming essential for banking and fintech environments. NUMR CXM separates identity from behavioral analytics, enabling advanced customer experience intelligence while maintaining strict BFSI data privacy compliance. By analyzing tokenized datasets instead of raw customer records, banks gain predictive insights without exposing sensitive financial identities.
We do not rely on standard SSL alone. We adhere to AES-256 encryption, the industry standard for top-secret data protection, across the entire data lifecycle.
Data Stage
Security Protocol
Data in Motion
All data moving from your client environment to NUMR infrastructure is encrypted via secure tunnels using state-of-the-art cryptography.
Data at Rest
Once data lands in our storage, it is immediately encrypted. It never sits on a disk in a readable format.
The Result
If a malicious actor were to bypass physical and network defenses, they would only see "gibberish." Without the keys, the data makes no sense.
This is where NUMR CXM distinguishes itself from generic SaaS tools. We understand that "trust us" is not a valid security policy for a bank.
We support a Bring Your Own Key (BYOK) architecture.
Architecture is only half the battle; operational rigor is the other. NUMR CXM is SOC 2 compliant, meaning our security controls, availability, and confidentiality protocols are not just internal policies - they are independently audited realities.
For BFSI decision-makers, this is the "fast pass" for procurement. It proves that our internal governance matches our external encryption standards, significantly streamlining your Vendor Risk Assessment (VRA) and onboarding timelines.
A common fear among BFSI leaders is vendor lock-in and data retention risks: "What happens to my data if I stop using NUMR?"
We have engineered a rigorous Data Purge Protocol.
Guidance referenced by the European Union Agency for Cybersecurity emphasizes that minimizing retained data significantly reduces long-term cyber risk and compliance liability.
NUMR CXM’s cryptographic data purge capability ensures that customer information does not persist beyond operational necessity. This strengthens GDPR compliance, limits exposure to future breach scenarios, and supports a lifecycle-based approach to financial data protection and CXM security governance.
Most CX tools are built for retail or e-commerce, where a data leak is a PR problem. NUMR CXM is built for BFSI, where a leak is an existential threat.
Feature
Generic CX Tools
NUMR CXM
Encryption
Standard SSL/TLS
AES-256 (Motion & Rest)
PII Handling
Often stored raw or lightly masked
Advanced Tokenization
Key Management
Vendor managed (You trust them)
BYOK (You trust yourself)
Data Deletion
Soft delete / Archiving
Cryptographic Purge
Don't compromise security for intelligence. Have both. Ready to see how top-tier banks are predicting churn and driving revenue without risking a single byte of data?
Schedule a Deep Dive with our CX architects.
Q: Does NUMR CXM store my customers' actual account numbers?
A: No. We recommend tokenizing sensitive fields before they even reach our analytics engine. Even if raw data is sent, our ingestion layer encrypts it immediately using AES-256 standards.
Q: Can we host NUMR CXM on-premise or in a private cloud?
A: Yes. We support hybrid deployments to ensure data residency requirements are met for specific banking regulations.
Q: Who holds the encryption keys?
A: With our BYOK (Bring Your Own Key) capability, you do. We process the data, but you hold the keys to the kingdom.
Q: Is your platform compliant with GDPR and local financial data laws?
A: Absolutely. Our architecture (Tokenization + Encryption + Purge capabilities) is designed specifically to facilitate compliance with GDPR, CCPA, and strict banking data norms.
In the high-stakes world of Fintech and Banking, security is the bedrock of trust. At NUMR CXM, we treat your data with the same rigor you treat your customers' deposits.
By combining PII tokenization, AES-256 encryption, and BYOK protocols, we ensure that your path to "Customer Centricity" never compromises your "Security Posture." Convert your leads, retain your customers, and protect your reputation all at once.